My article, “Improving Windows Logging Visibility in Elastic,” was featured in issue #82 of Detection Engineering Weekly, a newsletter by Zack Allen that highlights developments in Detection Engineering. In the article, I explain how to implement Sysmon to enhance logging visibility within Elastic. I also illustrate how default telemetry often leaves out basic details and how Sysmon can create a more comprehensive view of system activities.

✨ Swathi Tadepalli ✨
Cybersecurity Professional |
swatadepalli@gmail.com |
LinkedIn |
Github |
Medium
Woman in tech with a passion for Cybersecurity!
Resume | Projects
💻 Experience 💻
Amtrak
Cybersecurity Analyst
September 2023 - May 2024
- Designed and tuned detections within MS Sentinel, analyzed security logs for threats, helped implement a cybersecurity mesh architecture with Zero Trust, and supported threat intelligence with OSINT and access management.
IRS
IT Specialist
January 2021 - November 2021
- Conducted data mining with SAS, built .NET applications, ran SQL queries in TOAD to spot discrepancies, and reviewed IT tax project specs for accuracy.
GSA
Chief Privacy Office Intern
June 2019 - August 2019
- Reviewed privacy assessments, ensured GSA website compliance, analyzed web traffic with Google Analytics, and edited public-use forms with Google App Script.
📚 Education 📚
University of Maryland, Baltimore County
December 2019
Bachelor's in Information Systems
University of Maryland, Baltimore County
August 2024
Master's in Cybersecurity
Here's the time I...
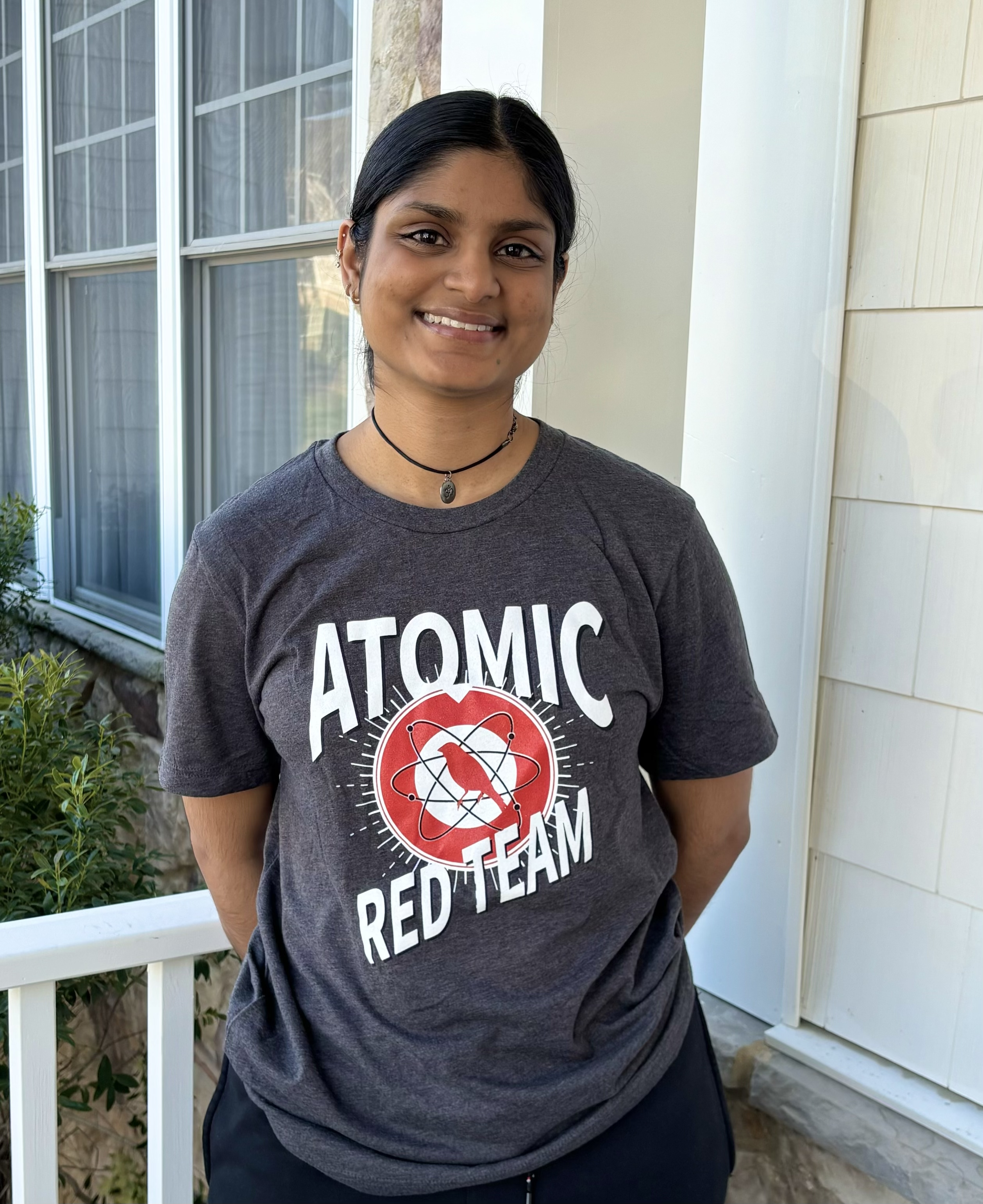
Atomic Red Team is an open-source library of scripted attack techniques designed to simulate real-world adversary behaviors based on the MITRE ATT&CK framework. I chose to test technique T1219 - Remote Access Software, by writing a PowerShell command to silently download and install RustDesk, an open-source remote desktop application. (My main motivator being the cool t-shirt!!)
In late 2023, Okta experienced a breach in which a malicious actor accessed files for 134 customers by stealing credentials stored on an employee's work laptop. The employee's use of Chrome's password manager, which saves passwords locally and can be easily decrypted, allowed the attacker to gain unauthorized access. Inspired by this incident, I decided to test the attack on my own account by using an open-source Python script to decrypt and display saved credentials in clear text.